TeamViewer is free for private use. Companies have to pay for the service. And with that service we may encounter a problem: The whole connection is established via the TeamViewer Server. Something is in the middle. Should we care of that? It’s all encrypted. My answer is: Yes, you should think about it.
First, remember the Public/Private Key and Digital Signature procedures.


Ok. Now let’s take a closer look to the establishment of a connection by two computers via TeamViewer.
Step 1
Link: https://dl.tvcdn.de/docs/en/TeamViewer-Security-Statement-en.pdf
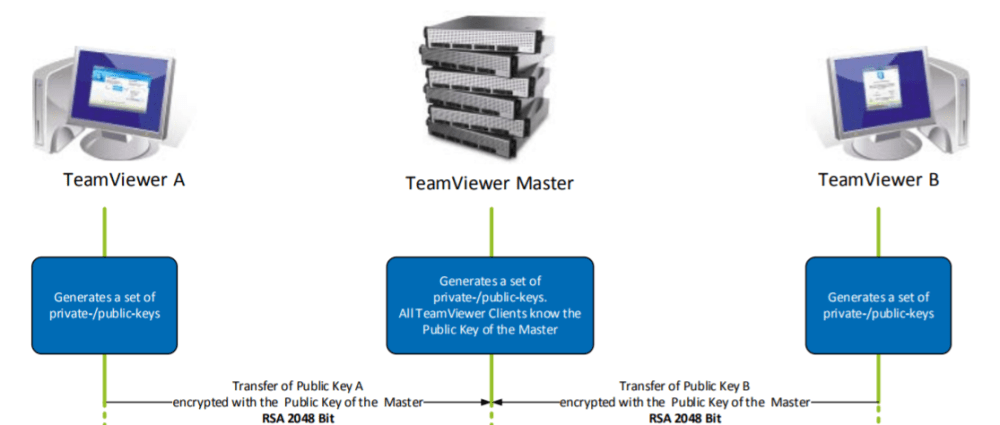
A and B generate a key pair. The master receives the public keys from A and B. So far, so good …
Step 2


Wouldn’t that be the master server who knows damn much about A and B and controls all negotiations and transfers. Consider the following, little realistic, but not impossible scenario …
Man-in-the-Middle-Attack originating from the TeamViewer Master against both Computers
- Computer A requests the Public Key B from the Master.
- However, the Master does not send the Public Key B, but a falsified Public Key Y to Computer A.
- Computer A generates a symmetric key W, which is required for communication between A and B, and encrypts it with the falsified public key Y, instead of the public key B.
- Computer A tries to send the packet to Computer B via the Master. Computer A has to pass the master, because Computer A and Computer B have a connection to the master and not among each other!
- But the Master stops the packet. Since the packet has been encrypted with the public key Y, the master can decrypt it with the private key of Y and therefore get the “secret symmetric key” W. The Master then encrypts it again with the actual Public Key B and signs it with another falsified Private Key X.
- The Master sends the data to Computer B.
- Computer B asks the Master for the public key of Computer A to verify the signature and the Master doesn’t return the public key of Computer A, but a fake public key Z.
- And so the whole thing goes on and on … All communication can be read by the master …
Conclusion
This time I refuse saying: “Have fun playing with TeamViewer”. 😉
Categories: Cyber Security