I’m happy many of you liked my little, humble script that enables you to play around in Active Directory. Well, this blog post will be a short one, because all I wanna do is to show you how to start it comfortably from your Client Computer. This avoids logging on to a Domain Controller and is a user-friendly feature for my community out there.
Starting Point
I assume that you have placed the tool in the right folder, as described in my first article AD Overview Graphical Tool: Active Directory Domain Services Section.
First, we’ll do some checks to make sure everything works out.
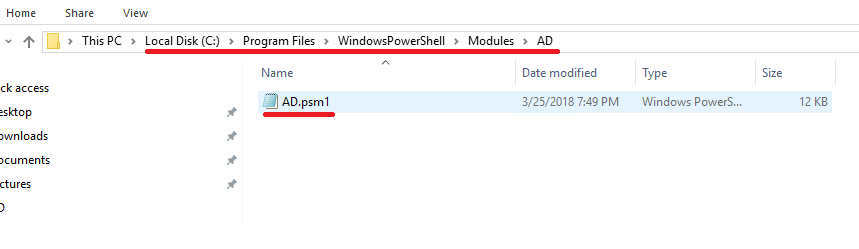
We should find the script (ad.psm1) on the Domain Controller at this place:
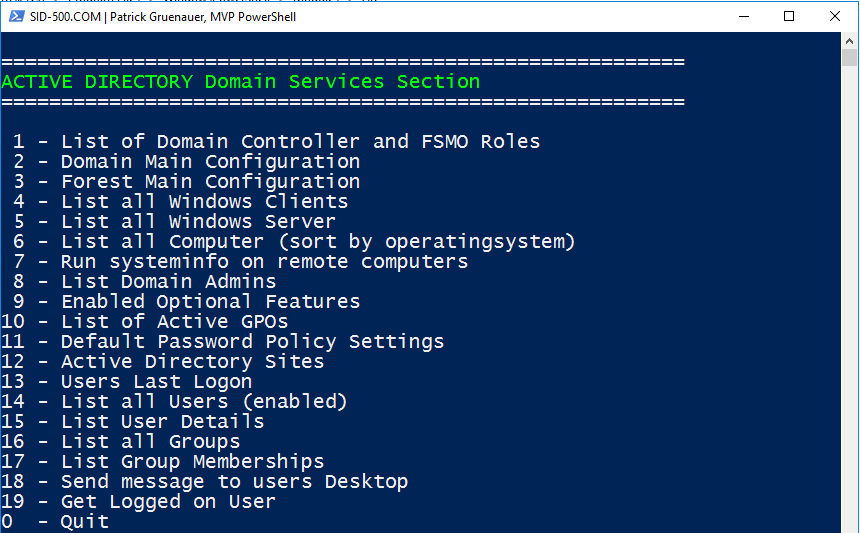
To be on the safe side, it should be possible to start it:

Ok, all tests done. Now we need a Client.
Starting the script from a domain-joined Active Directory Client (Windows 7/8/10)
The trick is to connect to the server using Enter-PSSession and then call the tool remotely. Note that you have to edit the server name.
Here’s the script:
$cred=Get-Credential
$ad=New-PSSession -ComputerName dc01 -Credential $cred
Invoke-Command -Session $ad -ScriptBlock {ad}
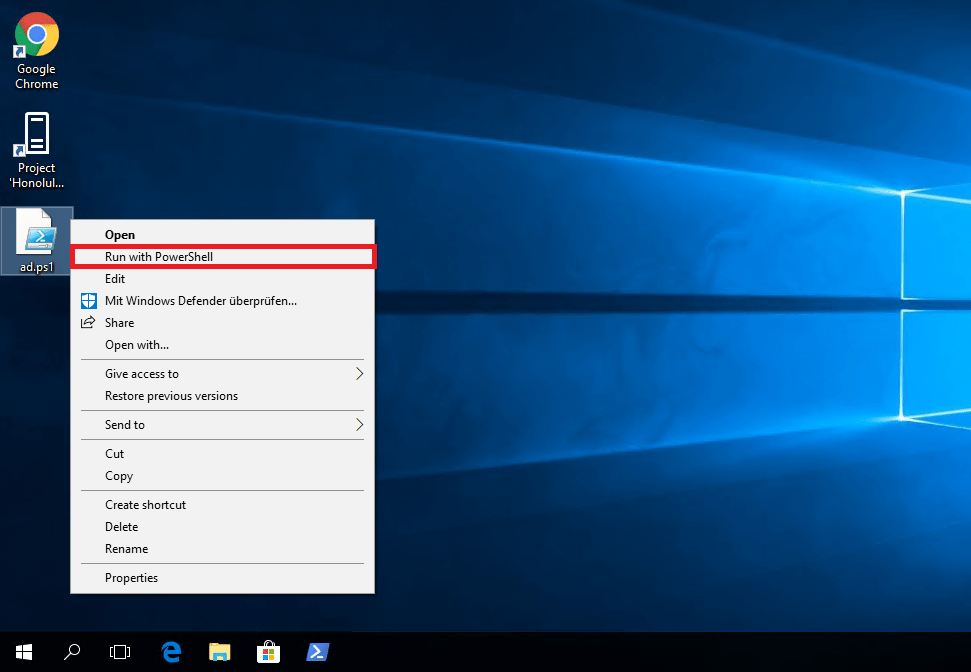
Open Notepad. Save it wherever you like and name it AD.ps1. Important Note: If you are always working with your Domain Admin account on the client then you can omit Line 1 and the Credential Parameter in Line 2.
Right-click the script and select Run with PowerShell …
You may be asked to change the PowerShell Execution Policy which is set to Restricted on all Windows Client Operating Systems by default. Click Y.
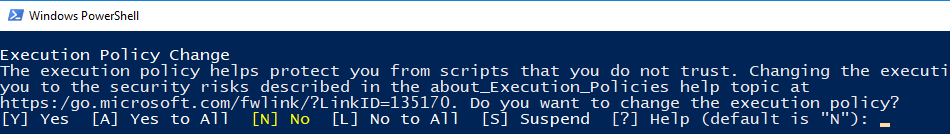
If you are faced with any other errors, check your Execution Policy, otherwise jump to the next screenshot.
Get-ExecutionPolicy
Set it to unrestricted and try again. Don’t worry, the execution policy was never meant to be a security feature in the strict sense, but a feature to avoid mistakes by the administrator. Remember that everyone can easily bypass the Execution Policy by running “powershell yourscript.ps1 -ExecutionPolicy Bypass”.
Set-ExecutionPolicy Unrestricted
Let’s move on.
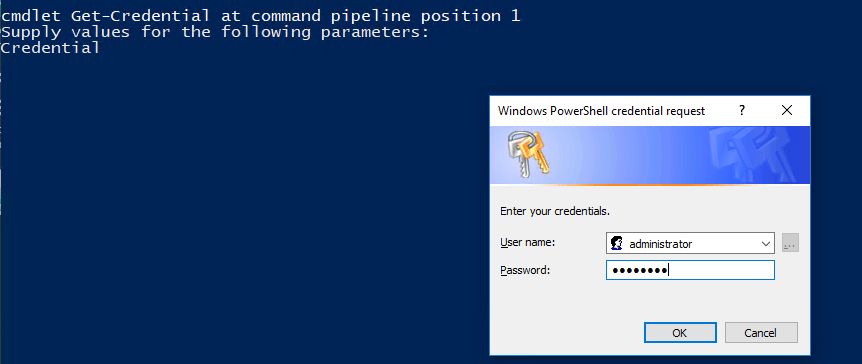
Now enter your domain admin credentials to connect to your domain controller.
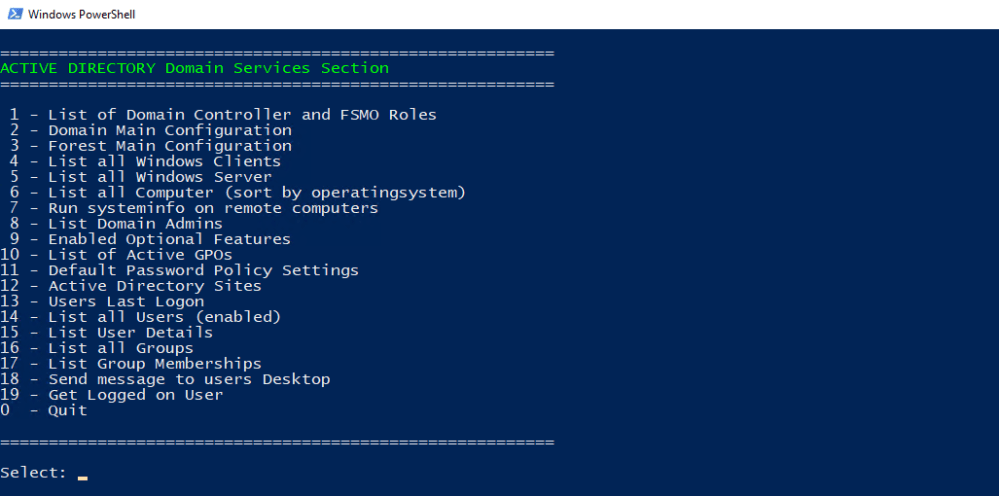
Woooh you’re there …
I wish all my readers a nice week.
Categories: PowerShell, Windows Server




Hi,
The script and all around the script was tested in a Windows Server 2012/2016 environment. You should be able to run this on W2k8, but with limitations.
Best,
P
LikeLike
How can I configure this script on a Windows Server 2008?
LikeLike