There is a small and useful group policy setting where you can enable monitoring of PowerShell, in particular the use of commands related to PowerShell modules. So, I tried it out and I want to keep this knowledge for my readers and for me in form of this blog post.
Activating Module Logging by using Group Policy Console
Before we begin, a quick note: You can activate logging on user or computer level. The difference is obvious: If you configure the setting for the computer, then logging for all user will be enabled. In PowerShell or cmd type gpedit.msc. This opens the graphical user interface of the local Group Policy Settings.
gpedit.msc
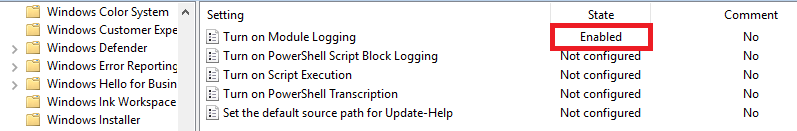
Navigate to Computer Configuration – Administrative Templates – Windows Components – Windows PowerShell and double-click “Turn on Module Logging”.

Here you can specify your logging settings for each PowerShell Module.
Let´s try it out. I click on Enabled and in the Options section i click on Show … I want to log all events of the PowerShell Module NetTCPIP. So, in the value field I enter NetTCPIP.

Then I click OK twice. The setting changed to Enabled. That looks good.
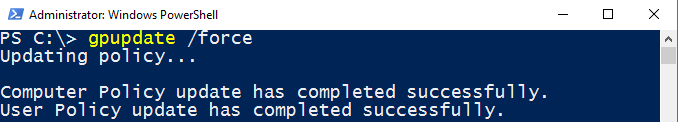
Finally, I run gpupdate /force to update the previous configured Group Policy Setting.
gpupdate /force
Wow, I have configured logging on computer level. Now I call the shots. 😉
Advice 1: You do not know all the module names by heart? What the hell, why not? 😉 Ok, I see, then run
Get-Module -ListAvailable | Select Name
to find out all names.
Advice 2: To monitor all PowerShell commands just enter * instead of the module names.

Testing the Configuration
From now on, the following must happen: If I run a command related to the module NetTCPIP, then the system must log this event in Event Viewer.
For testing, I run
Get-NetIPAddress
Then I open Event Viewer (eventvwr). And find this:

Big Brother is watching you.
Activating Module Logging by using PowerShell
Another method to activate Module Logging is using PowerShell. The following command activates Module Logging for the Active Directory Module (only available on Domain-Controllers or Computers which have RSAT installed):
Import-Module ActiveDirectory (Get-Module ActiveDirectory).LogPipelineExecutionDetails = $true (Get-Module ActiveDirectory).LogPipelineExecutionDetails

Well, let´s run a command from my blog post PowerShell: My top 10 commands for documenting and monitoring Active Directory.
Get-ADDomainController -Filter * | Format-List Name,Ipv4Address,IPv6Address,OperatingSystem
Once executed i find this in Event Viewer:

Note, that the setting configured by this way is effective only in the current session.
Happy monitoring!
See also
PowerShell: My top 10 commands for documenting and monitoring Active Directory
Categories: PowerShell




Hi Patrick,
Can I follow the same procedure to log events on a DC when the power shell commands ran on an workstation. If not could you please share how to do that.
Thanks
Rajesh
LikeLike
Hallo! What have you tried so far?
LikeLike
This is also something I am interested in. PS commands will executed on another server on our DCs.
LikeLike