In this post I want to introduce my top 10 commands for documentation and monitoring Active Directory Domain Services.
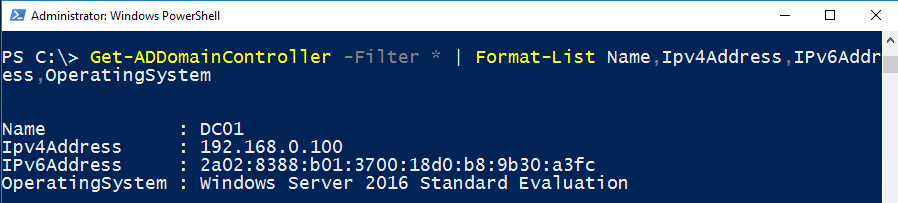
List all Domain-Controllers
Get-ADDomainController -Filter * | Format-List Name,Ipv4Address,IPv6Address,OperatingSystem
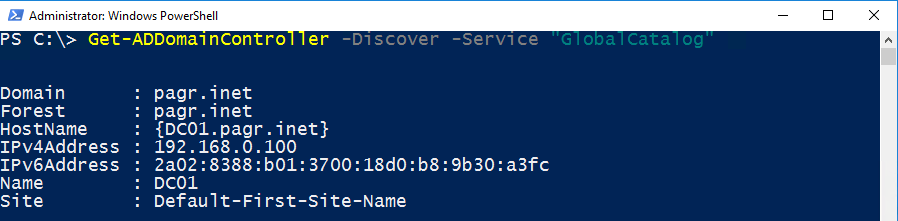
List all Global Catalog Servers
Get-ADDomainController -Discover -Service "GlobalCatalog"
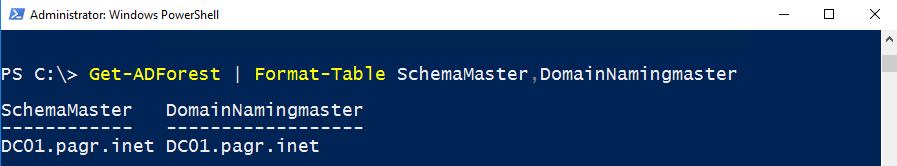
List all Operation Master Roles (FSMO)
Forest-wide Roles
Get-ADForest | Format-Table SchemaMaster,DomainNamingmaster
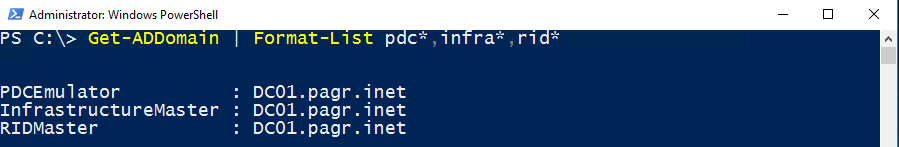
Domain-wide Roles
Get-ADDomain | Format-List pdc*,infra*,rid*
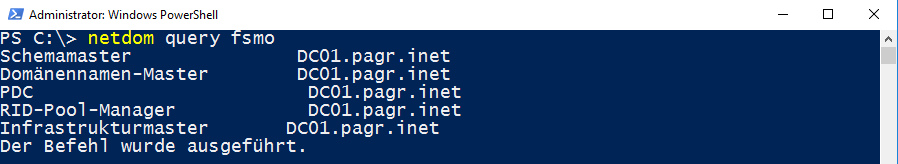
I have to admit: netdom query fsmo is much simpler 😉
netdom query fsmo
Link: Active Directory FSMO Rollen (Betriebsmaster)
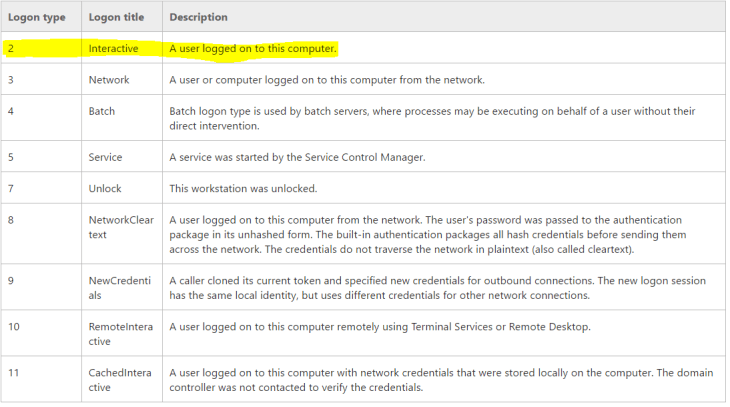
Monitoring Active Directory Logins
Successful Logins
I am looking for logins of user “Petra”. Note that all event logs on all domain controllers need to be looked up. If you don´t speak German, don´t let yourself get confused of the German screenshot. Pay attention to the Logontype “Anmeldetyp”. The value is 2 – a user has logged on to the domain.
Get-EventLog -LogName Security -InstanceId 4624 | Where-Object Message -match "petra" | Format-Table TimeGenerated,Message -AutoSize -Wrap

Unsuccessful Logins
Get-EventLog -LogName Security -InstanceId 4771 | Where-Object Message -match "petra" | Format-Table TimeGenerated,Message -AutoSize -Wrap

Note the error code 0x18. The user has provided a bad password.

More information about active directory logins in my German blog post: Active Directory Anmeldungen überwachen
Find orphaned Computer Accounts
To find all computer accounts that have not logged on to the domain for a year run
Get-ADComputer -Filter * -Properties operatingsystem,lastlogondate | Where-Object {($_.operatingsystem -notlike "*Server*") -and ($_.lastlogondate -le ((Get-Date).adddays(-365)))} | Sort-Object Lastlogondate | Format-Table Name,Lastlogondate

Link (German): Active Directory: Verwaiste (inaktive) Computerkonten finden
Find orphaned User Accounts
To find all user accounts that have not logged on to the domain for a year run
Get-ADUser -Filter * -Properties LastLogonDate | ? {$_.lastlogondate -ne $null -and $_.lastlogondate -le ((get-date).adddays(-365))} | Format-List Name,LastLogonDate
Link (German): Active Directory: Inaktive Benutzer mit Get-ADUser suchen
Find orphaned Group Policies
To find all Group Policies that have not linked to an organizational unit run
Get-GPO -All | % {
If ( $_ | Get-GPOReport -ReportType XML | Select-String -NotMatch "<LinksTo>" ) {
Write-Host $_.DisplayName, $_.CreationTime, $_.Modificationtime
}
}
Link (German): Active Directory: Suche nach inaktiven, nicht verknüpften Gruppenrichtlinien
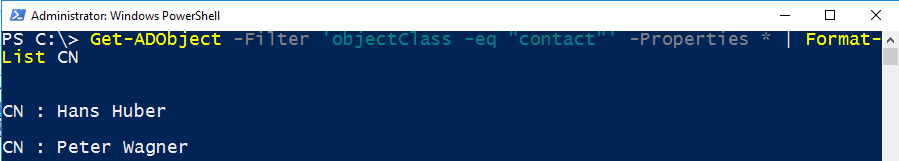
Find all Active Directory Contacts
Get-ADObject -Filter 'objectClass -eq "contact"' -Properties CN | Format-List CN
Link: PowerShell: Finding Active Directory Contacts
List Hardware Information of domain joined Computers
Get a list of all computers using Set-Content or a variable.
(Get-ADComputer -Filter *).Name | Set-Content C:\Computers.txt
Then run Get-WMIObject and save the output user-friendly.
Get-WMIObject -ComputerName (Get-Content C:\Computers.txt) -Class Win32_Computersystem -ErrorAction SilentlyContinue | ConvertTo-Html Name,TotalPhysicalMemory -Title (Get-Date) -Body "RAM Liste aller Computer" | Set-Content C:\Ram.htm
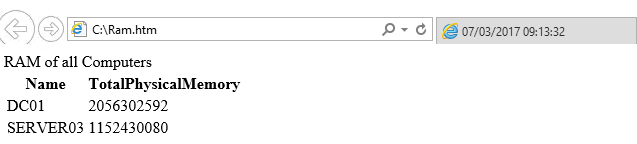
Link (German): WMI: Hardwarekonfiguration aller Domänen-Computer abrufen und speichern
Searching for Active Sync users
Fair enough this is related to Exchange. But Exchange is related to Active Directory. So lets search for Exchange Active Sync users.
Get-CASMailbox -Filter {hasactivesyncdevicepartnership -eq $true -and -not displayname -like "CAS_*"} | Get-Mailbox | Format-List name

Link (German): Exchange Active Sync Benutzer anzeigen
Further Information
If you want to install a Domain Controller with PowerShell, then take a look to my post PowerShell: How to install a Domain Controller with Server Core.
Categories: PowerShell, Windows Server




Looking for the last know user of a domain computer
Can the script be specific to list just 1 single computer
This is what I have so far
Get-ADComputer -Filter * -Properties * | Sort LastLogonDate | FT Name, LastLogonDate -Autosize | Out-File C:\ComputerLastLogonDate.txt
LikeLiked by 1 person
Hi, not possible. AD Computers do not store the last login date of a user.
LikeLike
Excellent Article keep up the good work.
LikeLike
Thank you!
LikeLike