Since Windows Server 2008, Domain Administrators are able to configure password polices per user and per group. This article shows how to set up password policies (Password Setting Objects) with PowerShell.
Prerequisites
Make sure your domain is running Domain Mode 2008 or higher. All Domain Controllers must run Windows Server 2008 or higher and the Domain Mode must be set to Windows Server 2008. For checking open PowerShell and run
Get-ADDomain | Select-Object Domainmode

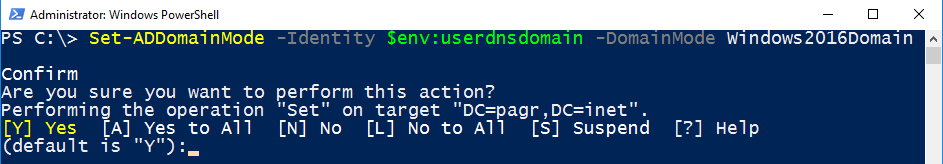
To change the domain mode, run Set-ADDomainMode. Don’t worry about the domain name. We get the name from the environment variable. Example (Windows Server 2016 Domain Mode):
Set-ADDomainMode -Identity $env:userdnsdomain -DomainMode Windows2016Domain
Introduction
The Default Domain Policy
Sure you know the purpose of the default password policy which is part of the the Default Domain Policy:
Get-ADDefaultDomainPasswordPolicy

This policy is mandatory for all Active Directory Users. Let’s configure new policies for particular users and/or groups.
The Active Directory Administrative Center (dsac.exe)
First of all: Of course, you can configure password polices by using the graphical interface. Run dsac to open the Active Directory Administrative Center. Navigate to System – Password Settings Container and click on New. Here you can configure your Password Settings using the graphical interface.
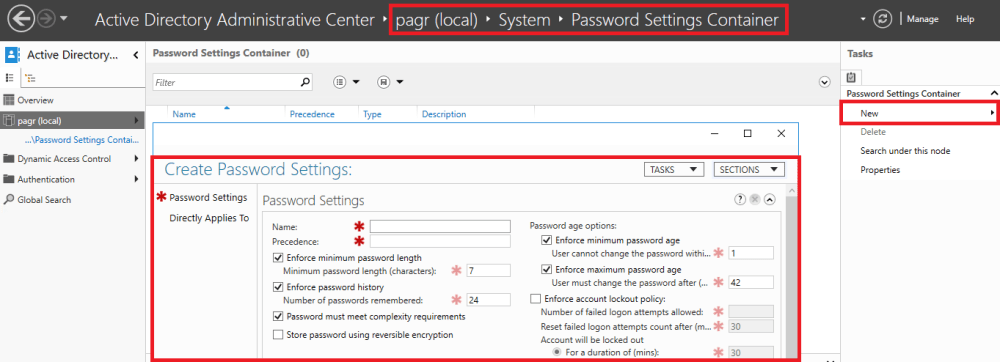
But in this article it’s all about PowerShell. 😉 Real men don’t click.
Configuring Fine Grained Password Polices with PowerShell
Suppose it’s the goal to configure a more restrictive policy for the members of the HR group. We want to set the minimum password length to 10 characters. (default: 7). To do so we can use the New-ADFineGrainedPasswordpolicy cmdlet.
New-ADFineGrainedPasswordPolicy -Name "HR_length_10" -MinPasswordLength 10 -Precedence 1

Pay attention to the mandatory parameter precedence. If multiple policies are configured, then the policy with the lowest precedence is used. Which means: The lower the number, the higher the precedence. More about it later.
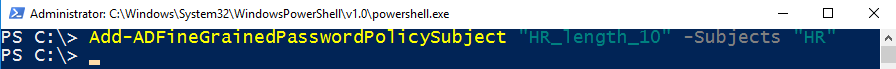
Adding Fine Grained Password Policies to users or groups
Now, the previous configured password object must be assigned to the HR group.
Add-ADFineGrainedPasswordPolicySubject "HR_length_10" -Subjects "HR"
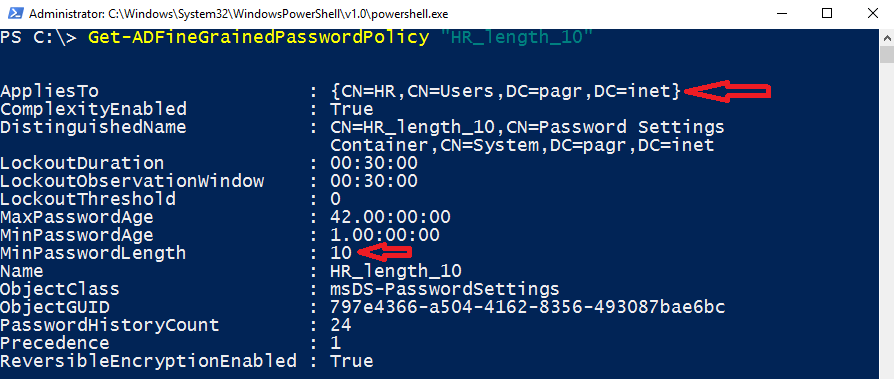
Checking the configuration
Now we are going to do some checks.
Get-ADFineGrainedPasswordPolicy
Let’s see what we have configured.
Get-ADFineGrainedPasswordPolicy "HR_length_10"
Get-ADGroup
Get-ADGroup "HR" -properties * | Select-Object msDS-PSOApplied
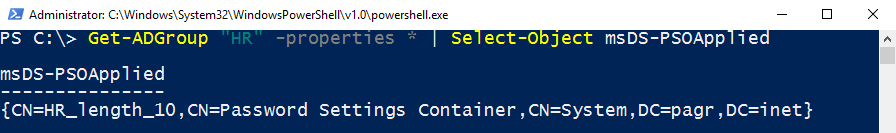
That looks good. The policy is assigned to the HR group.
Playing with Precedence Orders (msDS-ResultantPSO)
As mentioned, we can use precedence orders. The lower the number, the higher the precedence. Let’s configure another PSO for the HR group and set the precedence to 10 and configure a password length of 20.
New-ADFineGrainedPasswordPolicy -Name "HR_length_20" -MinPasswordLength 20 -Precedence 10
Add-ADFineGrainedPasswordPolicySubject "HR_length_20" -Subjects "HR"
Now we have configured 2 password policies. Both are assigned to HR.

Which of them is used? Remember, Petra is a member of the HR Group. Let’s have a look at petras account. And the winner is …
Get-ADUserResultantPasswordPolicy petra

Or check the msDS-ResultantPSO Attribute:
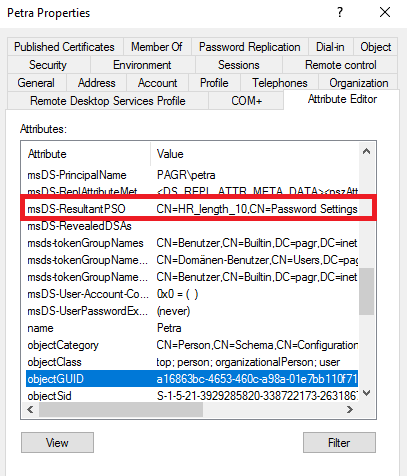
The lower the number, the higher the precedence …
For changing the Default Password and Lockout Policy which applies to all users see my blog post Active Directory: Changing Default Password and Lockout Policies
Have fun playing with password policies!
See also
PowerShell: Changing Active Directory user logon names (Bulk)
Securing Active Directory: Who can add computers to the domain? Only the domain admin. Are you sure?
Categories: Cyber Security, PowerShell, Windows Server




Just add the (minimum) rights you need to run any of these commands. Don’t assume everyone runs as Domain (or even Enterprise) Admin
LikeLike
Run Get-ADUser to find all your users and then run Get- ADUserResultantPasswordPolicy with the user logon name. If your user is not found, then the problem is probably a wrong user name.
LikeLike
Hi,
I have created FGPP, and targeted to two accounts in my organization grouping them to a security filter. if i view in attribute editor i can see applied POS as my FGPP but i cannot validate them with powershell command get-adusersultantpasswordpolicy, it says user cannot be found. also i tried another command NET USER Username / Domain, this shows the default domain policy applied to users.
LikeLike
Thank you Patrick. This one just saved me from setting up local accounts on 3 computers.
LikeLike
Thx for your feedback.
LikeLike