After the fourth part PowerShell for Beginners (Part 4): The PowerShell Help (Get-Help), we arrive at one of the most important topics: The Execution Policy. But before we will take a look at this feature the answer of the fourth exercise. We will also do a quick review what we’ve learned so far in Part 4.
All parts of the series can be found here: PowerShell for Beginners (Series)
Review (Part 4)
Exercise
In the fourth part I asked:
What is the 4th example of help for the command start-process? Once you’ve found it, run it on your computer!
Well, there are many ways to find this 4th example. One way is (provided you’ve downloaded the full help in the 4th part of this series) to use the local help files:
Get-Help Start-Process -Examples

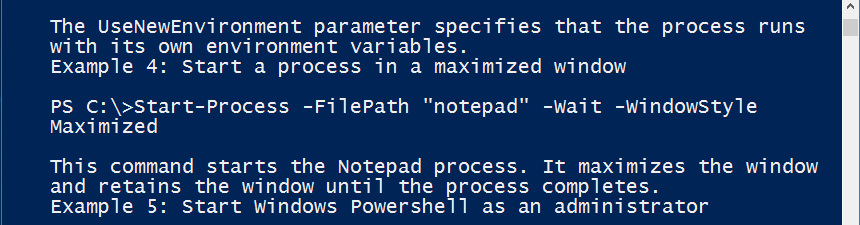
The fourth example shows how to start a notepad process. Copy and paste this command into your console and run notepad with PowerShell!
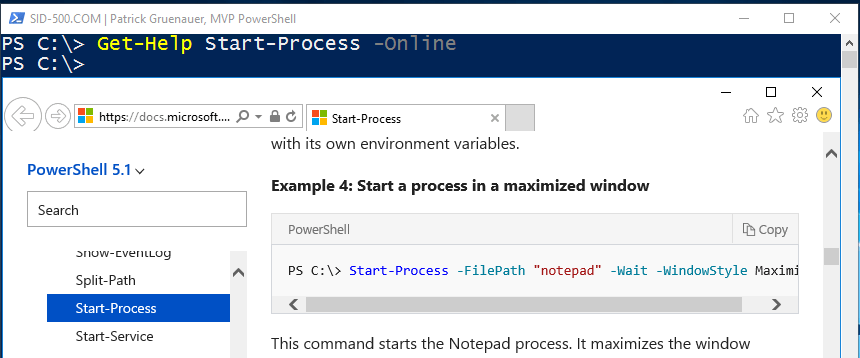
Another option is using the Online Help.
Get-Help Start-Process -Online
And the third option is to use the detailed parameter that show you much more than the examples.
Get-Help Start-Process -Detailed
The fourth option is using the full help.
Get-Help Start-Process -Full
Summary
The examples are a great source to learn PowerShell by learning by doing. They can be displayed by using the online help or by using the examples parameter.
The full help displays the whole help topic. The detailed help shows detailed parameter descriptions and examples.
The PowerShell Execution Policy
Now we come to the fifth part and this part is all about the PowerShell Execution Policy. What the heck is the Execution Policy? You download a script from the internet and want to execute it. The script has the extension. ps1. Red letters fill the screen. Red is usually not good. Yellow is ok, but red?
Almost every PowerShell book starts with two basic topics: Using the PowerShell Help (we’ve dealt with this in the 4th part) and the presence of a security feature called ExecutionPolicy. And both topics are essential for getting started with PowerShell. The PowerShell Execution Policy prevents the execution of ps1 scripts. For security reasons.
Windows 10 by default prevents the execution of PowerShell script files by default. Windows Server 2012/2016 allows the execution of self-made scripts by default, but all other scripts must be signed by a trusted publisher.
What are ps1 files?
PS1 files are PowerShell script files. A script is a program of instructions. Like batch files in cmd. You certainly remember the good old batch files.

Here’s an example of a PowerShell script.

What have we learned so far?
When dealing with scripts be aware of the PowerShell Execution Policy. The Execution Policy could prevent you from running PowerShell scripts. PS1 files are PowerShell script files.
Execution Policy Default Settings
Windows Client Editions (Windows 8 | 10)
The default value for Windows 10 is Restricted. That says, that no scripts are allowed, not even your own. You can check the setting with the command Get-ExecutionPolicy.
Get-ExecutionPolicy

Windows Server Editions (Windows Server 2012 | 2016)
The default value for Windows Server Editions is RemoteSigned. That means that you can run your own scripts and scripts from trusted publishers.

Review
There are differences between the Client and the Server Editions. On Client Editions the execution of scripts is not allowed by default. On Server Editions you can run your own scripts and digitally signed scripts from trusted publishers by default. Get-ExecutionPolicy shows the status.
Creating a ps1 file
Well, this series is practice-oriented. So let’s create a ps1 file in PowerShell that allows us to play with the execution policy.
First we create a new file with New-Item.
New-Item -ItemType File -Path C:\Temp -Name ps_script.ps1

Now let’s put a command into the file. Let’s say we want to call the date with Get-Date. For this we use the Add-Content command.
Add-Content -Path C:\Temp\ps_script.ps1 -Value 'Get-Date'
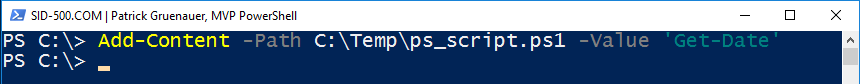
So now let’s do quick check with Get-Content if everything went well.
Get-Content -Path C:\Temp\ps_script.ps1

Fine. We have an example script. This script runs Get-Date.
What have we learned so far?
New-Item creates a ps1 file. The content commands adds, removes and modifies content.
Playing with Execution Policy
With this simple example file we are now able to start playing. Let’s explore the behavior. The execution policy is set to Restricted. See what happens. Note the white line.
… cannot be loaded because running scripts is disabled on this system …

Changing the Execution Policy
I will now change the execution policy with Set-ExecutionPolicy to RemoteSigned.
Set-ExecutionPolicy RemoteSigned

… and run the script again …

Surprise … surprise , this works.
Review
Set-ExecutionPolicy changes the behavior of the policy. The most restrictive setting is Restricted (default Windows 10). RemoteSigned (default Windows Server) allows you to execute your own scripts and scripts from Trusted Publishers.
The Execution Policy Values
RemoteSigned is the default setting on Windows Server 2012/2016 and Restricted is the default setting on Windows 8/10.
The four – from my point of view – most important execution parameters are:
- Restricted: No scripts may be executed.
- AllSigned: All scripts must be signed by a trusted publisher, including your own.
- RemoteSigned: All scripts from the Internet must be signed by a trusted publisher.
- Unrestricted: Runs all scripts.
There’s more. You can also define a scope for this values which can be found here:
More about digital signing in my blog post How to digitally sign PowerShell Scripts
Bypassing the ExecutionPolicy
Yeah, you read right. It is possible to bypass the policy. There are many ways to do this. I will show one of them. Note that the execution policy is set to Restricted.
powershell.exe -ExecutionPolicy Bypass -Command "c:\temp\ps_script.ps1"

Remember:
The execution policy is not a security system that restricts user actions. Users can easily circumvent the policy. Instead, the Execution Policy helps users establish basic rules and prevent them from accidentally violating them.
Review
The most important Execution Policy values are Restricted, Unrestricted, RemoteSigned and AllSigned. The Execution Policy is not a security system. Users can easily bypass the Execution Policy.
Here’s a great link that shows 15 ways to bypass the Execution Policy:
https://blog.netspi.com/15-ways-to-bypass-the-powershell-execution-policy/
Exercise
That’s it for today. Here’s the exercise up to the next part.
Change the execution policy that all scripts from the Internet must be signed. Try running a script you created yourself. What happens then?
The solution can be found in the next part.
See you at the next article PowerShell for Beginners (Part 6): PowerShell Profiles and the ISE
Patrick Gruenauer, MVP PowerShell
Categories: PowerShell




Hello Patrick, how are you today?Please do you help me> you said in your post above net use z:\\dc01\share. I have a problem with this command. I have file server name is bel01, and shared folder Razmena. When I put in notepad net use Z: \\bel01\Razmena this doesn`t work. What`s wronh with this command.
LikeLike
Without error message it’s impossible to identify the problem
LikeLike
I really appreciate how to create a script
thanks a lot
LikeLiked by 1 person