I’ve experienced that many people deliberately disable the Windows firewall. They don’t want to get annoyed with it, if something don’t work as expected. But there’s nothing to worry about, because it works as it should. I rather suspect that some administrators lack some knowledge. Any way, let’s get a list of all Domain Computers running Windows Server and let’s find out if they have their firewall enabled. It’s a small function which shows the good ones in green. The red ones are the bad ones 😉
In my previous article Configuring Windows Firewall with PowerShell I’ve described some basic firewall to-dos. Now we move a step further with a function which tests all Firewall settings of all domain-joined Windows Servers …

The Goal
One simple command. No parameters. A quick check of all domain-joined Windows Server. That’s the goal for this blog post. Here we go:


There were particularly brave people at work. You can’t buy courage. 😉
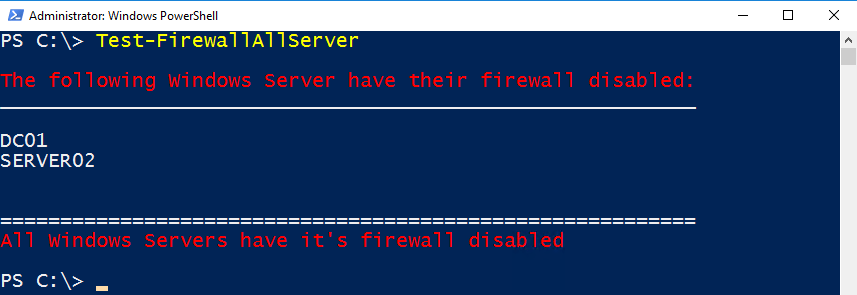
Function Test-FirewallAllServer
If you like the above, then keep on reading. Below you find the code.
Notes:
- This was tested on Windows Server 2012 and above
- Ensure you run the command on a Domain Controller or a computer with RSAT (ADDS) installed
- Make sure you have a cleaned up Active Directory environment (no orphaned Windows Server computer accounts). The script contains the erroraction parameter which ignores powered off servers.
- Ensure that Remote Management is enabled on all servers (since Windows Server 2012 it’s enabled by default)
Open PowerShell ISE. Copy the code into your session.
function Test-FirewallAllServer {
$servers=(Get-ADComputer -Filter * -Properties Operatingsystem | Where-Object {$_.operatingsystem -like "*server*"}).Name
$check=Invoke-Command -ComputerName $servers {Get-NetFirewallProfile -Profile Domain | Select-Object -ExpandProperty Enabled} -ErrorAction SilentlyContinue
$line="__________________________________________________________"
$line2="=========================================================="
$en=$check | ? value -EQ "true"
$di=$check | ? value -EQ "false"
If ($en -ne $null) {
Write-Host ""; Write-Host "The following Windows Server have their firewall enabled:" -ForegroundColor Green; $line; Write-Output ""$en.PSComputerName"";Write-Host ""
}
If ($di -ne $null) {
Write-Host ""; Write-Host "The following Windows Server have their firewall disabled:" -ForegroundColor Red ; $line; Write-Output ""$di.PSComputerName""; Write-Host ""
}
If ($di -eq $null) {
Write-Host $line2; Write-Host "All Windows Servers have it's firewall enabled" -ForegroundColor Green; Write-Host ""
}
If ($en -eq $null) {
Write-Host $line2; Write-Host "All Windows Servers have it's firewall disabled" -ForegroundColor Red; Write-Host ""
}
}
Make it permanent
Create a folder in C:\Program Files\Windows PowerShell\Modules. Name the folder Test-FirewallAllServer. Save the script there as psm1 file. Make sure the directory name and the file name are equal.
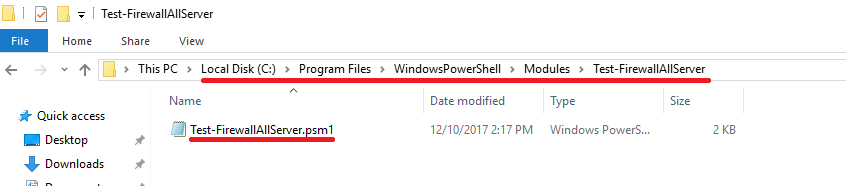
Close Windows PowerShell. Open PowerShell again. The command is now available for all users.
That’s it for today. Enjoy discovering Windows Firewall settings …
Categories: Cyber Security, PowerShell, Windows Server




Hi Patrick
Just a comment about your code. Do you know the sentence “filter left, format Right” ?
Get-ADComputer -Filter * -Properties Operatingsystem | Where-Object {$_.operatingsystem -like “*server*”}
Must be replaced by
Get-ADComputer -Filter {OperatingSystem -like “*server*} -Properties Operatingsystem}
It will be more efficient.
Regards
LikeLike
Thank you!
LikeLike
When I copy your script and run it in PS on a DC with RSAT (ADDS) installed then I don’t get a result and also no error.
What do i do wrong?
LikeLike
Can this also be used for Windows 10 desktops, by changing
Where-Object {$_.operatingsystem -like “*server*”}).Name
to something that will grab Windows 10 machines?
thanks
LikeLike
Yes, sure.
LikeLike
Great Script! Thank you. You should probably use “Get-NetFirewallProfile -PolicyStore ActiveStore” for GPO controlled Firewall policies.
LikeLiked by 1 person
Initially at first glance this appeared to work perfectly, but I got a lot of false positives (we keep Windows Firewall turned off since we have use Cisco firewalls). Not the end of the world, and I haven’t taken the time yet to look into why.
LikeLike
Hi, do you have a script for 2008 and below?
LikeLike
Unfortunately not. You can try to use netsh.
LikeLike
Worked like a charm for me and was exactly what I needed: A quick and easy way to verify that Windows Firewall was turned on everywhere.
LikeLike
Enjoy it!
LikeLike
Great ! I tested and I confirm that it perfectly works
Thansk a lot
SImone
LikeLiked by 1 person